PNNL: AI Effort Moves from Novelty to Front Lines of National Lab’s Cyber Protection
RICHLAND, Wash., March 26, 2026 — A research effort to explore how artificial intelligence can offer an advantage to cyber defenders has made the leap into computing operations at the Department of Energy’s Pacific Northwest National Laboratory.
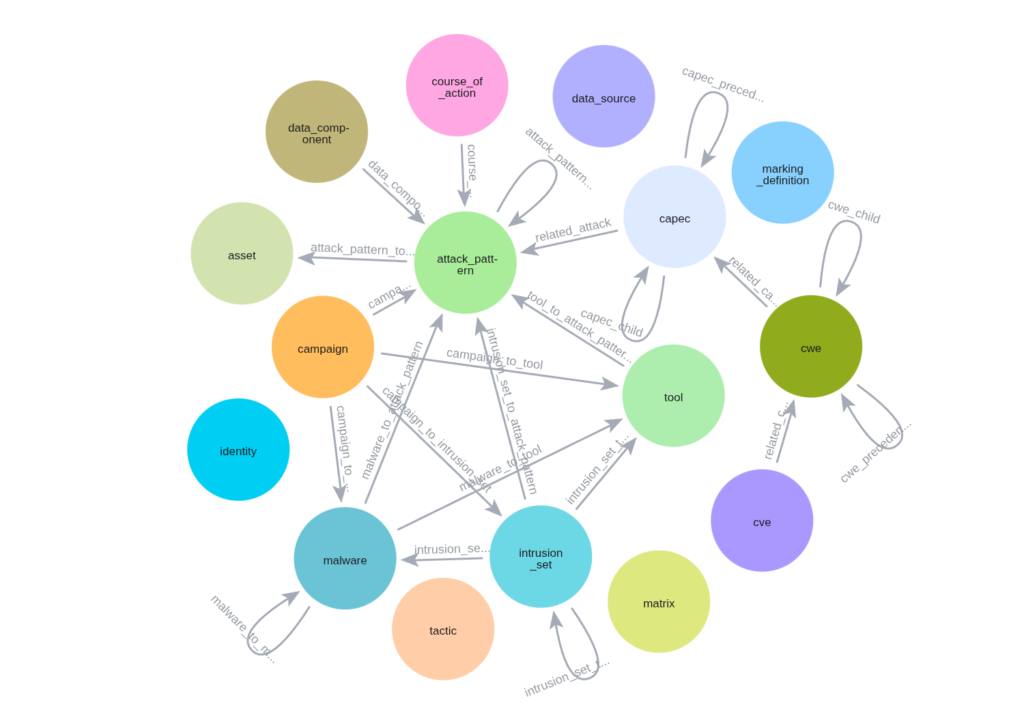
The PNNL program knits together thousands of data points into a stream of data that protects computing systems. Illustration credit: Mahantesh Halappanavar, PNNL.
“Every large company has a vulnerability management life cycle for detecting and remediating issues over time, but new threats pop up constantly. How can our actions be triaged and prioritized? Which vulnerabilities are most likely to be exploited, which ones hold the most risk?” said Joseph Aguayo, deputy chief information security officer at PNNL and a partner in the new approach. “Our technology organizes the information and delivers it to your desktop multiple times a day so defenders can stay updated right up to the minute.”
The work being implemented by Aguayo’s operations team has its roots in research led by Mahantesh Halappanavar, a chief computer scientist at PNNL whose research using AI links several databases related to cybersecurity. His team used graph theory combined with AI to build bridges between databases and to train the program to extract key information while constantly adapting to new information and settings. The technology brings together available threat intelligence with the unique configuration of a company’s computing assets.
The award-winning basic research, first published four years ago, uses AI to connect several strands of independent information in the cyber world to create a free-flowing stream of data that better protects against unwanted intrusions into computing systems.
PNNL information technology professionals—the hundreds-strong team that keeps PNNL’s computing operations safe and stable day to day—evaluated Halappanavar’s research and decided to put it to the test on the PNNL network.
Early results are promising, with quicker identification of the most pressing threats and the instant creation of roadmaps that show likely attacks and how they can be stopped.
The new approach takes advantage of a blizzard of data available to defenders, all of it updated regularly:
These information sources, plus a mind-bending amount of daily news about cyber breaches and risks, is pulled together to give PNNL security officials a clear, unobstructed view of the biggest cyber threats they are likely to face. Once an attack is recognized, the system enables defenders to stop it more quickly.
AI Brings Clarity, Focus to Threat Intelligence
The transformation of AI research into active laboratory operations comes at a time when the Department of Energy has launched the Genesis Mission to accelerate discovery science and enhance national security and energy innovation through the power of AI.
“Our program consumes a huge amount of threat intelligence and breaks it down into useful nuggets of information that defenders can act on immediately,” said Aguayo. “This helps us know what the bad guys knocking on our door are doing and gives us insights to quickly determine whether their actions are relevant or not.”
One key area of focus: zero-day attacks that exploit previously unknown or undisclosed software vulnerabilities. Security teams rely on layered defenses to protect against broad attack categories, but they need real-time threat intelligence to adapt those defenses when zero-day attacks emerge and no patches exist yet.
The 2021 Log4Shell vulnerability showed how quickly attackers can act: More than 1 million attacks targeted networks worldwide within 72 hours of its public disclosure. The new system is designed to identify such high-profile attack campaigns quickly while also increasing detection of lower-profile but network-relevant threats.
“The threat surface is huge, as AI is unleashed by both adversaries and defenders. With a massive number of vulnerabilities and undisclosed exploits, it’s a much bigger underworld than we want to think about,” said Halappanavar. “With knowledge graphs and AI, we are much better prepared; we know exactly what we need to know in a specific situation and environment. We can accurately predict missing information as well.”
Aguayo added, “You size up the attacks and tactics, and you take stock of your network environment—your users, your endpoints, your assets. And then you bring those two sources together to ask, ‘What 10 things can I do today to protect my network?’”
The team has presented the work at several scientific conferences, including the 2025 IEEE International Conference on Data Mining and NODES 2025. The new technology, dubbed MERU—Multimodal Entity Relationship Unification for robust cyber defense—is available for licensing through PNNL’s Office of Collaboration and Commercialization.
From Sailing Ships to Steamships
Aguayo joined PNNL two years ago after holding executive cybersecurity positions at several large companies and federal agencies.
“The change to AI from more traditional technologies is like the age when the world transitioned from sailing ships to steamships,” said Aguayo. “People were very good at rigging up the sails and charting by the stars, but then a whole different world with new capabilities emerged. That’s where we are with technology. I wanted to be at a place like PNNL where leading researchers are leveraging AI in new ways to protect critical domains, including national security and the energy grid.”
In addition to Aguayo and Halappanavar, PNNL scientists Siddhartha Das and Moqsadur Rahman contributed to the research. This work is funded by the Department of Energy’s Office of Science.
Source: Tom Rickey, PNNL
Related