Walk into any modern home or office and you’ll find a quiet web of connected gadgets running in the background. The doorbell has a camera. The TV talks to streaming apps. Your watch tracks your heart rate. Even light bulbs and plugs now want to join the Wi‑Fi.
All of this convenience comes at a cost: more places where your data can leak, be copied, or be held for ransom. Most people don’t have the time or skills to constantly watch over every device, every connection, and every app update. That’s where AI-driven security is starting to do a lot of the heavy lifting.
Smart Devices Multiply, and So Do the Risks

Most smart gadgets were built to be simple to use, not to be perfectly secure. Many of them:
- Ship with default usernames and passwords that are never changed
- Run the same firmware for years without updates
- Talk to cloud servers that the user barely knows anything about
Add ten or twenty such devices to a network, and even a careful person will struggle to keep track of what is going on. A single weak camera, for example, can act as a stepping stone for an attacker who wants to explore the rest of the network.
This is the basic problem: we are adding complexity faster than humans can monitor it. AI security tools try to close that gap by watching patterns that our eyes would simply miss.
AI Helps You See What’s Really on Your Network
Most people can name their phone, laptop, and maybe their TV. Few can list every connected gadget on their Wi‑Fi. AI-based systems are getting better at mapping this maze.
They can:
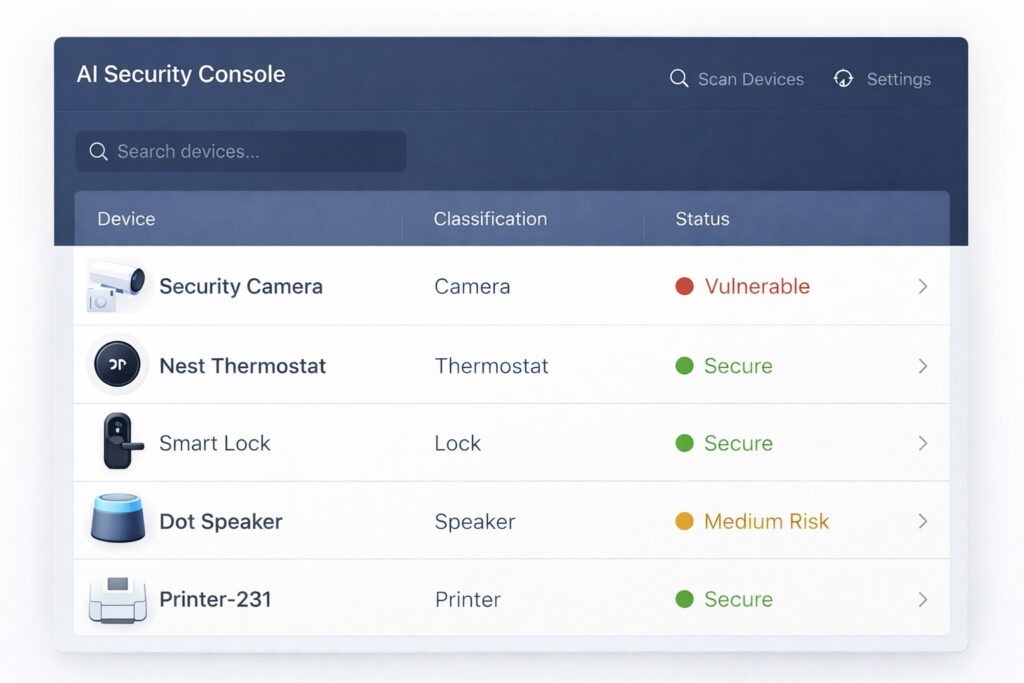
- Scan the network and sort devices into rough categories (camera, printer, thermostat, speaker, and so on)
- Notice when an unfamiliar device appears and starts talking on the network
- Learn what “normal” looks like for each gadget type over days and weeks
This kind of automatic inventory sounds basic, but it matters. If you don’t even know a device is there, you definitely aren’t securing it. Modern AI Security approaches treat this visibility as the first building block.
Spotting When a Gadget Behaves “Off”

Most attacks don’t announce themselves with a big red warning. They hide inside patterns that look almost normal. Instead of relying only on signatures and known malware, AI watches for subtle changes.
A few examples:
- A smart camera that usually uploads a small amount of data suddenly sends large video streams to an unknown server in another region
- A smart plug, which normally just reports power usage, begins reaching out to multiple internal devices
- A door lock sends repeated failed authentication attempts at odd hours
To a human glancing at logs, this might look like noise. A trained model, on the other hand, can say, “This is not how this device usually behaves,” and push an alert or even cut the connection automatically.
From Reaction to Prevention with AI Security
In the past, security often meant reacting: patching systems after a breach, adding rules after a new malware strain started circulating. With connected gadgets and 24/7 networks, that is too slow.
AI-driven defenses aim to shift things closer to prevention by:
- Learning from huge collections of past incidents and attack patterns
- Updating protections globally when new tactics are spotted elsewhere
- Turning those insights into concrete policies that apply to your environment
This is where structured AI Security platforms come in. They combine machine learning, threat intelligence, and enforcement tools so that when one customer gets attacked, others benefit from the lessons almost immediately.
Keeping Data Safer at the Edge
Many smart devices now process data directly on the gadget or on a local hub. This “edge” layer is often where the most sensitive information lives: live video from your home, audio from your living room, health statistics from your wrist, and so on.
AI is being used here in a few practical ways:
- Filtering and compressing data before it leaves the device, so less raw material is exposed
- Watching for tampering with settings, firmware, or physical connections
- Applying context rules, such as blocking remote access attempts at unusual times or from unusual locations
The goal is to reduce how much sensitive data has to travel across the internet and to stop suspicious behavior as close to the source as possible.
Responding Faster When Something Goes Wrong
No system is perfect, and sooner or later, something strange will happen on a smart network. The difference now is how quickly that “strange thing” can be noticed, understood, and contained.
AI assists incident response by:
- Pulling together clues from different logs and devices into a single story
- Assigning rough risk levels, so serious threats rise above background noise
- Triggering actions like isolating one device, blocking a specific IP address, or forcing stronger authentication
That doesn’t remove humans from the loop, but it does remove a lot of repetitive manual work—and cuts down the time attackers have to move around.
Walking the Line Between Security and Privacy

Whenever you say “AI is watching the network,” people worry about surveillance. That concern is valid. A sensible security approach acknowledges that and sets clear limits.
Modern practices try to:
- Only collect data that is necessary for detecting threats
- Encrypt data in transit and at rest
- Give admins and users simple ways to see what is being monitored and to adjust policies
Again, this is where mature AI security strategies matter. It’s not just about throwing algorithms at traffic; it’s about using them in a way that respects the people behind the devices.
Why AI Security Is Becoming Non‑Optional
The number of smart gadgets in homes, offices, factories, and cities is still climbing. Attackers know this. They are already using automation and, increasingly, their own AI tools to probe for weaknesses at scale.
Trying to defend such an environment with manual checks and static rules is like trying to guard a busy airport by watching one door. That’s why AI Security is moving from “nice to have” to “necessary” for any serious strategy.
It gives you:
- A clearer picture of every device on the network
- Early warnings when something behaves in an unusual or risky way
- Faster, more consistent reactions when a real threat appears
You may not see it or think about it every day, but in a world filled with connected devices, AI has started to become one of the quiet forces standing between your data and the people who want to abuse it.
Madhurima Nag is the Head of Content at Gadget Flow. She side-hustles as a parenting and STEM influencer and loves to voice her opinion on product marketing, innovation and gadgets (of course!) in general.

